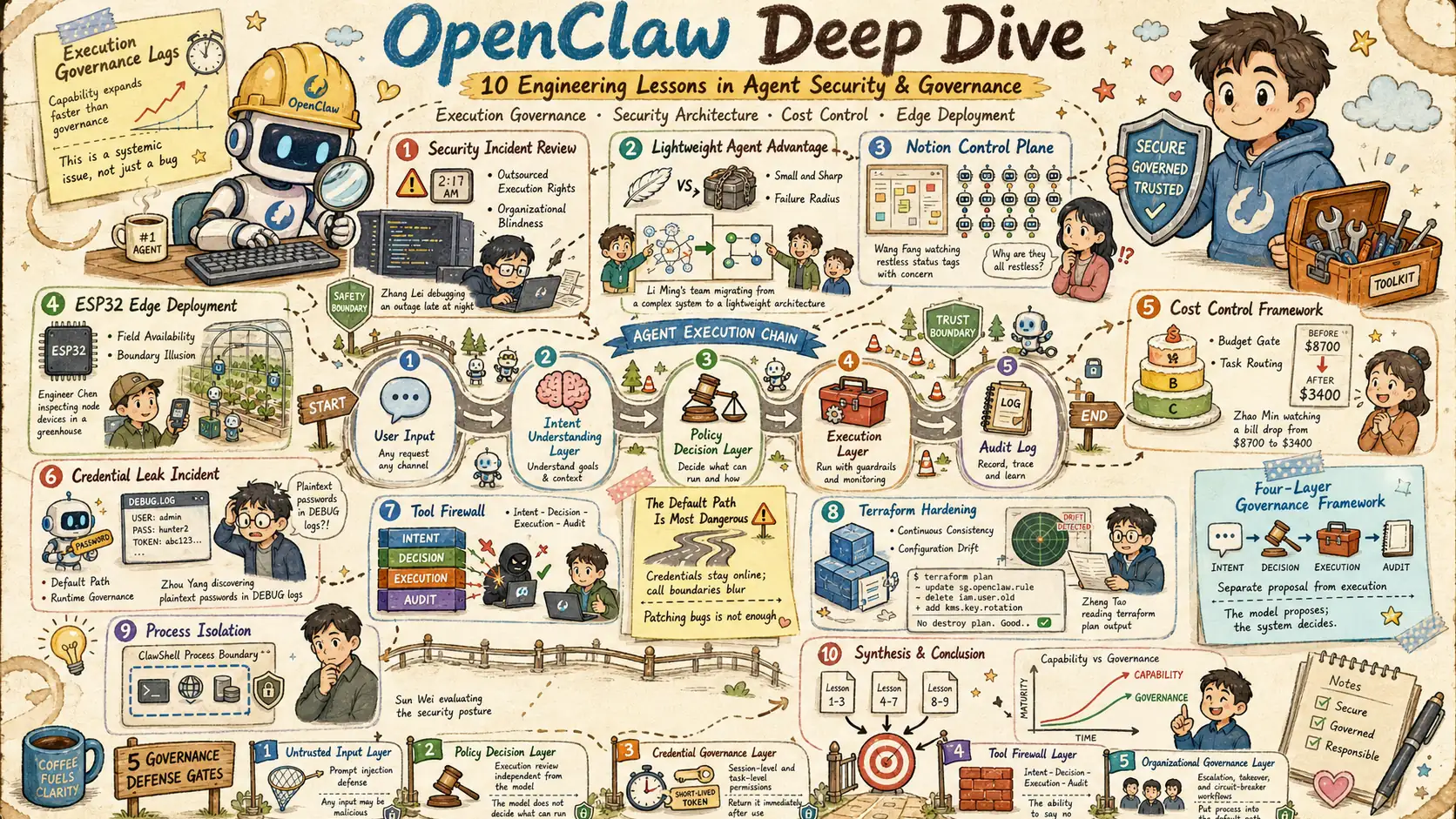
Series · OpenClaw security in-depth interpretation
OpenClaw in-depth interpretation
A series of original interpretations of issues surrounding OpenClaw security, agent runtimes, tool boundaries, and engineering governance.
Progress is stored in this browser only; without saved progress, reading starts from chapter one.
- Status
- Completed
- Difficulty
- Intermediate
- Chapters
- 10/10
- Read time
- 120 min
Guide
Series guide
Understand the reading promise, main path, and reference chapters before entering individual articles.
This series uses OpenClaw and related agent-runtime discussions as a lens for security, tool boundaries, operational risk, and engineering governance. The purpose is to help readers separate real architectural risk from hype, vendor framing, and single-incident overreaction.
Who should read this series?
- Engineers evaluating agent runtimes, tool sandboxes, and automation boundaries.
- Security reviewers who need concrete failure modes instead of generic AI safety language.
- Platform teams designing guardrails for credentials, tools, network access, and operator workflows.
Core security questions
The articles repeatedly return to five questions: what can the agent access, what can it execute, what evidence remains after an action, what boundary blocks escalation, and what operational playbook exists when the boundary fails. These questions make each incident or tool discussion comparable.
Reading order and article roles
Start with the incident-oriented chapters to see how small boundary mistakes become system risks. Continue with the contrarian and framework chapters to evaluate common claims against concrete architecture evidence. Use the later synthesis chapters as a checklist for tool firewalls, credential handling, Terraform hardening, and prompt-injection containment.
Series Path
Read by chapter
Chapter clicks store reading progress only in this browser so the series page can resume from the right entry.
- Original interpretation: Why do OpenClaw security incidents always happen after 'the risk is already known'? Why do OpenClaw security incidents always happen after 'the risk is already known'? This article does not blame the model for being out of control, but instead asks about the design flaws of execution rights: when the system puts execution rights, audit rights, and rollback rights on the same link, how does organizational blindness amplify controllable deviations into accidents step by step?
- Original interpretation: Why is the lightweight Agent solution likely to be closer to production reality than the 'big and comprehensive' solution? This is not a chicken soup article praising 'lightweight', but an article against engineering illusion: many OpenClaw Agent stacks that appear to be stronger only front-load complexity into demonstration capabilities, but rearrange the cost into production failures and early morning duty costs.
- Original interpretation: Treat Notion as the control plane of 18 Agents. The first thing to solve is never 'automation' This article does not discuss whether the console interface is good-looking or not, but discusses a more fundamental production issue: when you connect 18 OpenClaw Agents to the Notion control plane, is the system amplifying team productivity, or is it amplifying scheduling noise and status chaos?
- Original interpretation: Putting Agent into ESP32, the easiest thing to avoid is not the performance pit, but the boundary illusion. This article does not describe the ESP32 Edge Agent as a cool technology trial, but dismantles the four most common misunderstandings: running the board does not mean the system is usable, being offline is not just a network problem, and local success does not mean on-site maintainability. Edge deployments require new engineering assumptions.
- Original interpretation: When OpenClaw costs get out of control, the first thing to break is never the unit price, but the judgment framework. If OpenClaw API fee control only focuses on the unit price of the model, it will usually turn into an illusion of cheapness in the end: the book will look good in the short term, but structural waste will still quietly accumulate in the background. This paper reconstructs a cost framework including budget boundaries, task layering and entry routing.
- Original interpretation: When the Agent tries to 'take away the password', what is exposed is never just a leak point Rewrite 'Agent knows your password' into a more uncomfortable accident review: the real failure is not a certain encryption action, but the team's use of credentials as a default capability that is always online, constantly visible, and constantly callable. This article discusses runtime governance gaps.
- Original interpretation: Why what OpenClaw really lacks is not more prompt words, but a tool firewall that dares to say 'no' Many teams pin OpenClaw safety on prompt constraints, but what really determines the upper limit of accidents is not what the model thinks, but whether the system allows the model's ideas to be directly turned into tool execution. This article proposes a four-layer governance framework of 'intention-adjudication-execution-audit'.
- Original interpretation: It is not difficult to deploy OpenClaw to AWS. The difficulty is not to mistake 'repeatable deployment' for 'already safe' Dispel a very common but dangerous illusion: when teams say 'we've reinforced it with Terraform', they often just complete the starting point, but mistakenly believe that they are at the end. IaC can make deployment consistent, but it cannot automatically make OpenClaw systems continuously secure.
- Original interpretation: The real priority for Agent credential security is not 'where to put it', but 'who can touch it and when' Refuting an all-too-common misconception: OpenClaw credential security is complete as long as key escrow, encrypted storage, and rotation are done. The reality is just the opposite. The most likely place for trouble often occurs at runtime - not 'where' it is placed, but 'who can touch it and when'.
- Original interpretation: Looking at the three types of OpenClaw security articles together, it is not the vulnerabilities that are really revealed, but the lag in governance. When the three topics of prompt word injection, credential leakage, and tool firewalls are put on the same table, you will find that they point to the same core contradiction: OpenClaw's capabilities are expanding faster than execution rights management. This article synthesizes the common conclusions of three security articles.